Configure WinRM for HTTPS manually
Configuring for HTTPS involves following steps.
- Check whether WinRM service is running
- Create HTTPS listener
- Add firewall exception
- Validate HTTPS listener
Check whether WinRM service is running
PS C:\Temp> Get-Service WinRM
Status Name DisplayName
------ ---- -----------
Running WinRM Windows Remote Management (WS-Management)If the WinRM service is not running, you might need to configure WinRM using winrm quickconfig. When you configure winrm first time, it is configured to use 5985 by default.
check already registered listeners by running following command
PS C:\Temp> WinRM e winrm/config/listener
Listener
Address = *
Transport = HTTP
Port = 5985
Hostname
Enabled = true
URLPrefix = wsman
CertificateThumbprint
ListeningOn = 127.0.0.1, 172.20.20.1, ::1, fe80::5efe:172.20.20.1%15, fe80::d071:b058:c541:a212%12Create HTTPS listener
To create a HTTPS listener, you need to have a certificate.
Generate SSL Certificate with one of these options
- CA Authority(e.g:Versign)
- Active Directory Certificate Services (If using internal CA)
- Self Signed(Not to be used in Production)
- Run the following command to create https listener. (Using cmd)
winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Hostname="<YOUR_DNS_NAME>"; CertificateThumbprint="<COPIED_CERTIFICATE_THUMBPRINT>"}
C:\Users\Administrator>winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Hostname="dc01.winadmin.org";CertificateThumbprint="FCD7AF299FED777E467356DA67C66263AA805B9B"}
ResourceCreated
Address = http://schemas.xmlsoap.org/ws/2004/08/addressing/role/anonymous
ReferenceParameters
ResourceURI = http://schemas.microsoft.com/wbem/wsman/1/config/listener
SelectorSet
Selector: Address = *, Transport = HTTPSAdd firewall exception
You can use command and GUI tool to configure firewall exception.
Via command
# Add a new firewall rule
netsh advfirewall firewall add rule name="Windows Remote Management (HTTPS-In)" dir=in action=allow protocol=TCP localport=5986
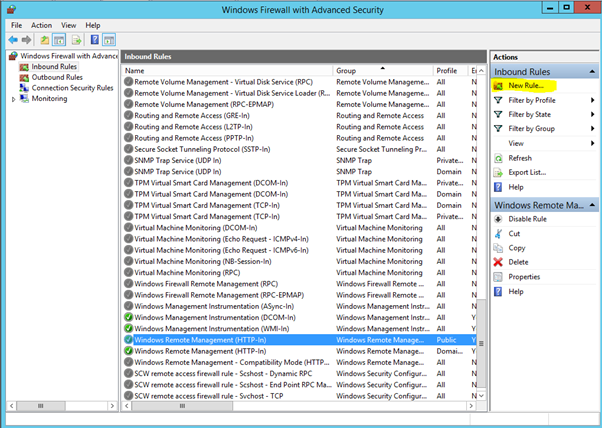
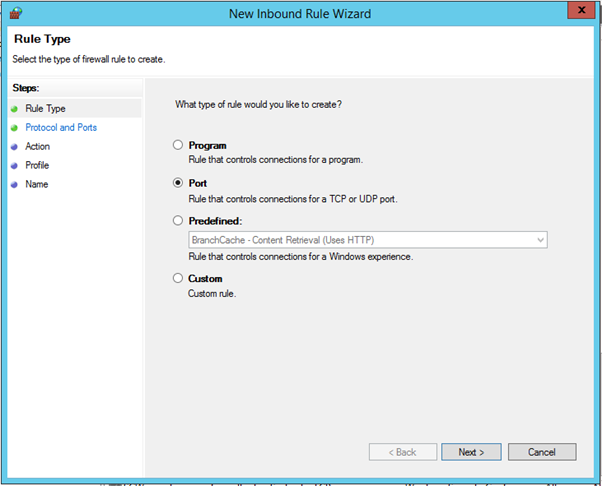
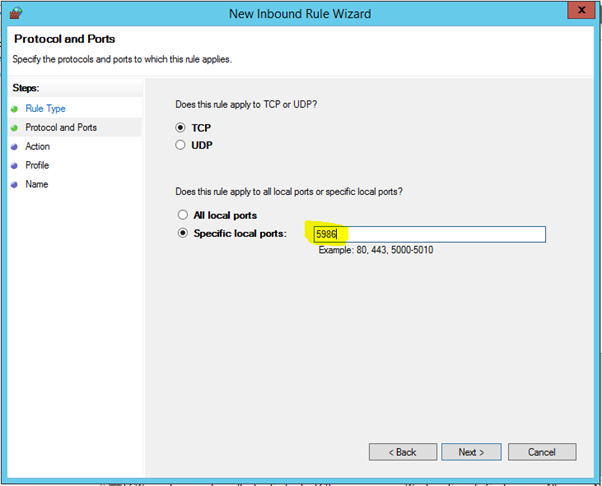
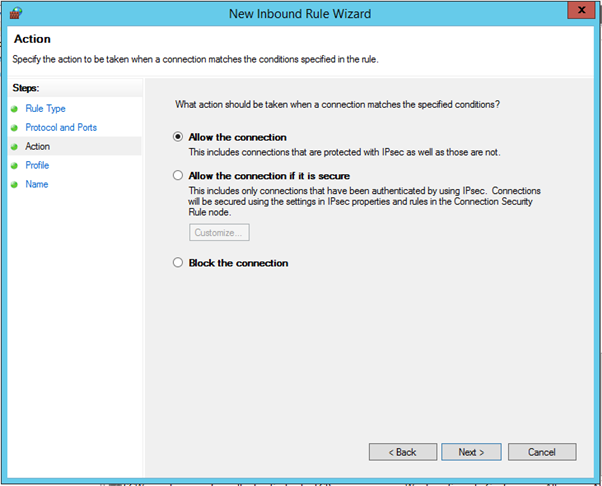
Using Windows Firewall with Advanced Security GUI tool.
Open Windows Firewall with Advanced Security and click New Rule.
Select Port
Specific local ports – Enter 5986
Select Allow the connection
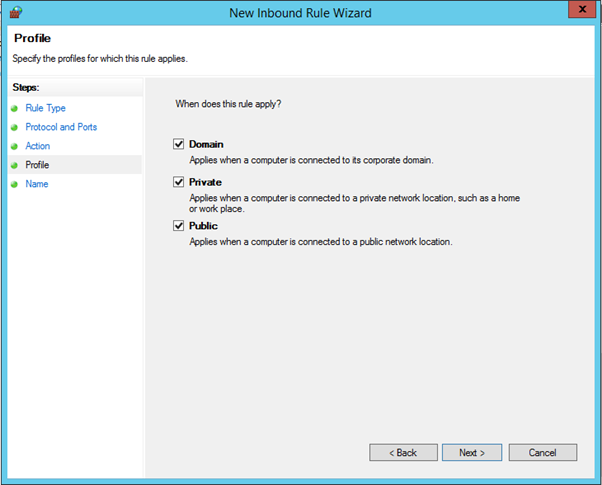
Select the options whatever is required
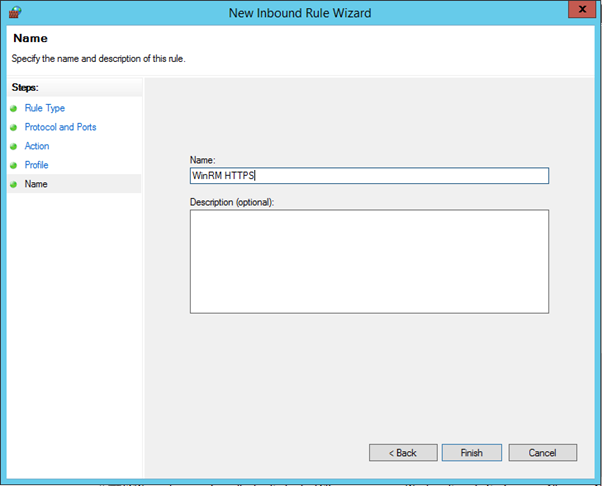
And give a name and click Finish
Now check the WinRM Listener. The output should be as follows.
C:\Users\Administrator>WinRM e winrm/config/listener
Listener
Address = *
Transport = HTTP
Port = 5985
Hostname
Enabled = true
URLPrefix = wsman
CertificateThumbprint
ListeningOn = 127.0.0.1, 172.16.1.101, ::1, fe80::1d72:b620:dc60:d783%4
Listener
Address = *
Transport = HTTPS
Port = 5986
Hostname = dc01.winadmin.org
Enabled = true
URLPrefix = wsman
CertificateThumbprint = FCD7AF299FED777E467356DA67C66263AA805B9B
ListeningOn = 127.0.0.1, 172.16.1.101, ::1, fe80::1d72:b620:dc60:d783%4Verify you can connect to the machine via HTTPS
PS C:\Users\Administrator> Enter-PSSession -Cn dc01.winadmin.org -UseSSL
[dc01.winadmin.org]: PS C:\Users\wintel\Documents>If you give only host name, it will give errors and will not connect.
PS C:\Users\Administrator> Enter-PSSession -Cn dc01 -UseSSL
Enter-PSSession : Connecting to remote server vc01 failed with the following error message : The server certificate onthe destination computer (vc01:5986) has the following errors:
The SSL certificate contains a common name (CN) that does not match the hostname. For more information, see theabout_Remote_Troubleshooting Help topic.
At line:1 char:1
+ Enter-PSSession -Cn vc01 -UseSSL
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidArgument: (vc01:String) [Enter-PSSession], PSRemotingTransportException
+ FullyQualifiedErrorId : CreateRemoteRunspaceFailed